CMMC 2.0 is not just a cybersecurity requirement—it is a system for proving organizational reliability, where success depends more on process maturity and evidence than on tools.
Most companies searching for “Demystifying CMMC 2.0” want a clear answer: What is it, and how do we comply?
Here’s the direct answer:
CMMC 2.0 is a three-level certification model required by the U.S. Department of Defense that verifies whether contractors can consistently protect sensitive data—and prove it through documented, auditable processes.
What Is CMMC 2.0? A Clear and Practical Explanation
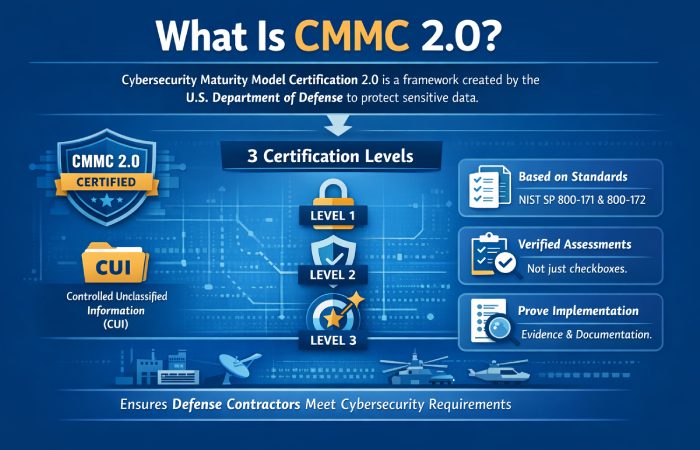
CMMC 2.0, or Cybersecurity Maturity Model Certification, is a framework introduced by the U.S. Department of Defense to ensure that contractors protect sensitive information, particularly Controlled Unclassified Information (CUI). It builds on established standards like NIST SP 800-171 and NIST SP 800-172, which are widely recognized across the cybersecurity industry.
Unlike traditional compliance systems that rely heavily on self-attestation, CMMC 2.0 introduces verification mechanisms. This means companies must not only implement controls but also provide evidence that those controls are consistently applied.
This aligns with broader cybersecurity principles promoted by organizations like the National Institute of Standards and Technology (NIST), ISACA, and the Cybersecurity and Infrastructure Security Agency (CISA), all of which emphasize governance, risk management, and continuous monitoring.
The Real Problem CMMC 2.0 Solves
At its core, CMMC 2.0 addresses a systemic issue: the vulnerability of the defense supply chain. Cyber attackers rarely target highly secured government systems directly. Instead, they exploit smaller contractors with weaker security practices.
Consider an illustrative example. A small subcontractor handling sensitive design data might use basic security tools but lack strict access controls or monitoring. An attacker breaches this vendor and gains indirect access to critical defense information. This “weakest link” problem is exactly what CMMC 2.0 aims to eliminate.
| Supply Chain Risk | CMMC 2.0 Response |
| Weak vendor security | Standardized control requirements |
| Inconsistent processes | Mandatory documentation |
| False compliance claims | Verified assessments |
| Lack of monitoring | Continuous compliance expectations |
The deeper insight here is important. CMMC 2.0 is not just about cybersecurity—it is about trust validation across an entire ecosystem.
Understanding the Three Levels of CMMC 2.0
CMMC 2.0 simplifies the previous five-level model into three levels. While this appears simpler, the practical demands remain significant.
| Level | Focus Area | Requirements | Assessment Type |
| Level 1 | Basic cyber hygiene | 17 controls | Self-assessment |
| Level 2 | Protection of CUI | 110 controls | Self or third-party |
| Level 3 | Advanced security | Enhanced controls | Government-led |
Level 1: Foundational Security
Level 1 focuses on basic cybersecurity practices such as password management and access control. It is suitable for organizations that do not handle sensitive information. While relatively simple, it offers limited strategic value.
Level 2: The Critical Bottleneck
Level 2 is where most organizations struggle. It requires alignment with NIST SP 800-171 and demands a high level of documentation, consistency, and audit readiness.
For example, a company may have strong technical controls but fail to document them properly. During an audit, the absence of evidence leads to non-compliance—even if the controls are technically in place.
Level 3: Advanced Security
Level 3 applies to organizations involved in highly sensitive national security work. It includes advanced requirements based on NIST SP 800-172 and involves government-led assessments. This level is less common but significantly more demanding.
CMMC 2.0 vs CMMC 1.0: What Changed in Practice
Although CMMC 2.0 reduces the number of levels and introduces flexibility, it does not necessarily reduce the effort required.
| Aspect | CMMC 1.0 | CMMC 2.0 |
| Levels | 5 | 3 |
| Assessment | Mandatory third-party | Hybrid model |
| Flexibility | Limited | Increased |
| Internal responsibility | Lower | Higher |
The key shift is subtle but critical. Responsibility has moved inward. Organizations must now maintain compliance continuously rather than relying solely on external audits.
The Biggest Misconception: Tools vs Evidence
One of the most common mistakes companies make is equating cybersecurity tools with compliance. While tools are necessary, they are not sufficient.
| Scenario | Compliance Outcome |
| Tools installed, no documentation | Fail |
| Documentation exists, not followed | Fail |
| Tools + documentation + consistency | Pass |
Auditors look for:
- Logs and records
- Policy enforcement
- Evidence of ongoing monitoring
This leads to a powerful insight:
In CMMC 2.0, evidence is more important than infrastructure.
Core Control Areas That Drive Success
Successful compliance efforts focus on a few critical domains rather than attempting to address everything at once.
| Control Area | Key Focus | Why It Matters |
| Access Control | Limit system access | Prevent unauthorized entry |
| Incident Response | Detect and respond | Reduce breach impact |
| Configuration Management | Control system changes | Maintain stability |
| Risk Assessment | Identify vulnerabilities | Enable proactive defense |
These areas form the foundation of a strong compliance program and align closely with guidance from NIST and CISA.
Documentation: The Hidden Challenge
Documentation is often underestimated but plays a central role in compliance. Organizations must create and maintain several key documents, including System Security Plans (SSPs) and Plans of Action & Milestones (POA&Ms).
The challenge lies in ensuring that documentation accurately reflects real-world practices. Many companies create policies that look good on paper but are not consistently followed.
| Documentation Element | Purpose | Common Failure |
| SSP | Defines security posture | Outdated or incomplete |
| POA&M | Tracks improvements | Not actively maintained |
| Policies | Set rules | Not enforced |
| Logs | Provide evidence | Missing or inconsistent |
A simple but effective framework is:
Document → Implement → Verify → Repeat
Cost of CMMC 2.0: A Realistic View
CMMC compliance involves both direct and indirect costs. While many businesses focus on tools and audits, the hidden costs often have a greater impact.
| Cost Type | Examples |
| Direct Costs | Tools, audits, consultants |
| Indirect Costs | Training, process redesign, internal time |
| Business Size | Estimated Cost Range |
| Small | $20,000 – $80,000 |
| Medium | $80,000 – $250,000 |
| Large | $250,000+ |
The biggest factor influencing cost is timing. Organizations that start early can spread investments over time, while those that delay often face expensive, rushed implementations.
Common Mistakes That Lead to Failure
Many compliance failures can be traced back to a few recurring mistakes:
- Treating compliance as a one-time project
- Ignoring documentation requirements
- Waiting until contracts demand certification
- Relying too heavily on external vendors
These mistakes reflect a deeper issue: a lack of operational maturity.
A Practical Framework to Achieve Compliance
A structured approach can significantly improve success rates.
| Step | Action | Outcome |
| 1 | Gap assessment | Identify weaknesses |
| 2 | Prioritize controls | Focus resources |
| 3 | Build documentation | Ensure audit readiness |
| 4 | Implement controls | Strengthen security |
| 5 | Monitor continuously | Maintain compliance |
| 6 | Simulate audits | Reduce risk |
This framework aligns with best practices recommended by NIST, ISACA, and CISA.
Small Businesses: Barrier or Opportunity?
CMMC 2.0 presents both challenges and opportunities for small businesses.
| Before Compliance | After Compliance |
| High competition | Reduced competition |
| Lower trust | Verified credibility |
| Limited contracts | Access to premium contracts |
While the initial investment may seem significant, achieving compliance can create a strong competitive advantage.
Future of CMMC 2.0
CMMC 2.0 is expected to evolve in three key ways:
- Increased enforcement tied to contracts
- Integration into procurement processes
- Adoption of automated compliance tools
These trends reflect a broader shift toward continuous, real-time cybersecurity management.

